As we move further into this digital era, businesses need to be as vigilant as possible with their cybersecurity compliance. There will always be new cyber threats and changes in regulatory laws.
Compliance is much more than simply paying fines. Compliance protects your customers’ private information and creates trust from your customers.
The landscape of regulatory compliance is continually being modified by lawmakers. Therefore, business entities need to stay informed about updates and adapt quickly to these changes.
Risk Management is an important part of achieving Cybersecurity Compliance. Risk Management is the process of identifying risks, evaluating them, and taking steps to mitigate or eliminate them.
Organizations that develop a strong cybersecurity model will be able to comply with those requirements. Long-term viability relies upon this.
GDPR and CCPA data protection laws have established elevated expectations regarding privacy. Failure to comply may result in a penalty.
The future of compliance is evolving. Cloud security and remote work challenges are at the forefront of cybersecurity compliance trends.
Adoption of next-generation strategies requires organizations to leverage emerging technologies such as artificial intelligence (AI) and machine learning (ML). Use of these technologies improves both the ability to detect threats and respond to them.

Summary
It’s important to note that the aforementioned article “Cybersecurity Compliance Trends” identifies current business approaches to evolving cyber threats and changing regulatory requirements. The most critical area addressed was how companies must comply with new and emerging data protection laws, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), and update their compliance programs as they continue to evolve.
Advanced technology solutions such as Artificial Intelligence (AI) and Machine Learning (ML) will aid compliance by leveraging data analytics to provide insights into organizational performance and increase automation efficiency. In addition to implementing AI and ML, the report indicates that many organizations are fostering cross-departmental collaboration to build a culture of security awareness, thereby reducing the risk of security breaches.
As organizations transition from traditional workplace environments to remote or hybrid workplaces, they face the challenge of developing flexible compliance strategies to ensure that employees accessing company data outside their offices have adequate protections. Ultimately, this report highlights the importance of staying up to date with evolving cybersecurity compliance trends to protect sensitive information, meet regulatory requirements, and maintain customer confidence in a rapidly changing digital environment.
Complete & Secure Identity and Access Management Tools for Cybersecurity Guide
The Evolving Landscape of Cybersecurity Compliance
Cybersecurity compliance regulations change daily. Each business must navigate the ever-changing regulations of its industry.
As we live in a globalized world, businesses operating across international boundaries must comply with many different regulations.
Companies that want to succeed in meeting these changing regulatory requirements must develop dynamic compliance strategies. Companies cannot implement static compliance strategies in today’s constantly changing compliance environment.
The main reasons why business is going to have to adapt to changing regulations and laws regarding cybersecurity compliance include:
- More regulatory oversight
- Evolution of the way technology works
- Increase in cyber attacks
To stay on top of the increasing number of cyber threats, businesses will have to be prepared to react quickly to emerging threats. A flexible compliance model is needed to enable organizations to remain adaptable and responsive to emerging threats.
Blockchain and Internet of Things (IoT) technologies are examples of how still-evolving technologies will create or change compliance obligations. Blockchain and IoT offer many opportunities but also present challenges.
The new environment requires an organization to develop a solid plan to handle all aspects of compliance. Developing a solid compliance plan means continuously monitoring and regularly assessing compliance-related procedures.

The time has come for compliance to evolve from a “one-and-done” process to an ongoing one. The first step will be to have an in-depth knowledge of all existing and new regulations.
Companies that understand how regulations change over time may gain a competitive advantage by enhancing customer trust and company reputation.
To successfully navigate the ever-changing regulatory landscape, companies must strike a balance between the need to innovate and the need to maintain compliance.
Cybersecurity Threat & Compliance Statistics
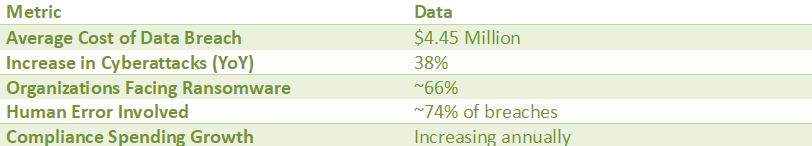
Key Insight: Rising threats are driving higher compliance investments globally.
Source:
- IBM Cost of Data Breach Report
https://www.ibm.com/security - Verizon Data Breach Report
https://www.verizon.com/business
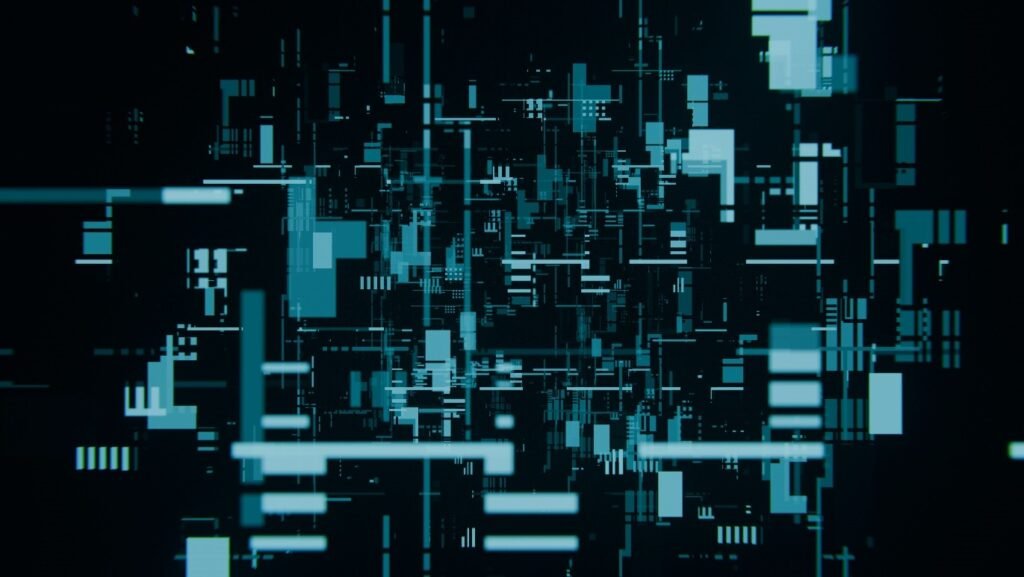
Cybersecurity Compliance: Cybersecurity compliance ensures businesses protect sensitive data and meet essential security standards

Cybersecurity compliance is an imperative necessity for every organization in the modern world of technology. The primary function of this compliance is to help protect sensitive data through the use of appropriate measures for complying with certain minimum requirements of security as well as regulatory requirements. Given the increasing frequency of data breaches and cyberattacks, cybersecurity compliance is vital to protecting company data.
In addition to fulfilling the legal responsibilities associated with cybersecurity compliance, companies that practice good cybersecurity compliance build trust within their customer base. Companies can successfully protect themselves from reputational damage by implementing robust cybersecurity compliance systems to minimize the risk of data breaches.
For businesses to be compliant with all aspects of cybersecurity, they must understand all applicable regulations for their industry. Regulations typically require data encryption, access control, and incident response. For example, regulations such as GDPR and HIPAA require high levels of data protection. Compliance with regulations is an ongoing process. Organizations need to continually monitor their security practices and improve them when necessary.
The key elements of cybersecurity compliance include identifying and mitigating your organization’s exposure to risk. Cybersecurity Compliance entails performing regular security audits. Implementing Multi-Factor Authentication (MFA) helps ensure access to critical assets is restricted and controlled. Establishing clear guidelines for how your organization will manage data ensures consistency in data-handling practices across all departments. Organizations that implement a combination of these security best practices will improve their overall cybersecurity posture and demonstrate their commitment to being compliant.
Implementing emerging technologies such as Artificial Intelligence (AI), Machine Learning (ML), and other automation tools further enhances an organization’s ability to comply with regulations. The use of AI and ML enables organizations to automate threat detection and response, thereby improving the efficiency of an organization’s compliance efforts. Additionally, by automating the compliance process, organizations can identify vulnerabilities and proactively remediate them.
Lastly, developing a culture of security is important for achieving effective cybersecurity compliance. Employees play a significant part in preventing breaches or reporting suspicious activity when training employees about their role in maintaining compliance is implemented. When employees understand why cybersecurity compliance is important, they are more likely to follow established policies and report potential security issues.
In summary, cybersecurity compliance is an ongoing effort requiring continuous focus from the entire organization. Prioritizing cybersecurity compliance allows organizations to safeguard sensitive data, support regulatory requirements, and establish trust with stakeholders.
To protect against increasingly sophisticated cyber threats, maintaining a robust compliance program is critical to the continued success of any organization competing in today’s global marketplace. Cybersecurity compliance goes beyond simply reducing fines and penalties; it protects an organization’s integrity and sensitive data.
Complete & Secure SOC 2 Compliance Checklist for Data Security
Regulatory Compliance: Regulatory compliance ensures businesses follow legal frameworks to maintain security and customer trust

Regulatory compliance is a key component of success in today’s increasingly regulated environment. Regulatory compliance protects sensitive data and fosters trust among customers; it creates a level of security that all organizations are accountable for upholding. Regulatory compliance has a great deal to do with how businesses operate, especially when they process personal and financial data.
Cybersecurity Compliance is one of the most important components of regulatory compliance. Cybersecurity Compliance requires that you implement the measures necessary to meet regulatory authority standards. Those items could be as simple as encrypting your data, securing your networks, and having incident-reporting policies in place, as required by law. When you prioritize regulatory and cybersecurity compliance, you will have an effective and secure way to protect your customers’ data.
Depending on the industry, non-compliance with regulatory compliance can result in serious repercussions such as large fines and loss of reputation. Companies subject to regulations such as GDPR and HIPAA are scrutinized extensively due to their data practices. Non-compliance places organizations at financial risk through fines and can damage their relationships with consumers, creating a need for organizations to focus on regulatory compliance.
Routine audit and assessment activities are an important aspect of maintaining compliance with government regulations. Conducted as part of a larger compliance strategy, audit and assessment activities allow companies to identify potential vulnerabilities and/or weaknesses in their current compliance approach. Companies have a responsibility to continually monitor compliance to ensure they remain compliant with ever-changing regulations.
The employee education and awareness process is also significant in meeting regulatory compliance requirements. When employees clearly understand the significance of following legal standards and how each employee’s participation will be used to support company-wide cybersecurity compliance efforts, it creates a strong organizational culture of compliance. This ultimately reduces the likelihood of breaches and strengthens the overall security posture.
In conclusion, regulatory compliance provides a foundation for business operations by ensuring adherence to applicable legal standards, protecting customer data, building customer trust, and providing an additional layer of protection against cybercrime. Regulatory and cybersecurity compliance enable businesses to secure valuable customer data while building customer confidence in the processes used to manage it.
As government regulations evolve, it is essential that all businesses remain vigilant and responsive in their compliance activities. Ultimately, regulatory compliance is more than simply complying with governmental regulations; it also provides a platform for a business to become a long-term, trusted entity in today’s increasingly complex digital environment.
Risk Management: Effective risk management helps organizations proactively identify, assess, and mitigate cybersecurity threats.

Risk Management is an important business strategy for companies seeking to successfully navigate the complex landscape of Cybersecurity Threats. Risk Management includes identifying, evaluating, and managing risks related to the Digital Landscape prior to a breach. As we continue through this rapid technological evolution of Cybersecurity threats, companies will need to be proactive in risk management to protect Data and Maintain Trust.
A key component of risk management is integrating Cybersecurity Compliance into Organizational Frameworks. Cybersecurity Compliance provides assurance that Organizations meet Regulatory Requirements and Industry Best Practices, which form the foundation of Risk Management. When Cybersecurity Compliance Initiatives are aligned with Risk Management Strategies, Organizations will have a greater ability to understand vulnerabilities (that may result in a Data Breach or other type of Cyber Incident).
To begin with, organizations should conduct comprehensive risk assessments. A comprehensive risk assessment will allow the Organization to identify Potential Cybersecurity Threats and evaluate the impacts those threats may have on Operations. By doing so, Organizations will be able to prioritize there Risk Management Efforts and allocate Resources appropriately. Additionally, Regular Assessments are necessary to maintain Cybersecurity Compliance, as they provide insight into the effectiveness of current Security Measures.
Once an organization has identified its risks, it can develop plans to mitigate them. Organizations must take multi-layered, proactive measures, such as firewalls, intrusion detection systems, and employee training programs, to successfully manage risk. In addition to enhancing security, these proactive measures will ensure the organization remains compliant with all relevant cybersecurity regulations.
Regulatory compliance plays a key role in developing risk management policies. When organizations adhere to established frameworks, they can be assured that their risk management practices align with industry standards and regulatory expectations. This alignment will not only improve an organization’s overall security posture but will also protect businesses from potential legal repercussions stemming from non-compliance.
Creating a culture of risk management within an organization is essential. Employees should understand the importance of cybersecurity compliance and their role in reducing organizational risks. By promoting awareness and accountability, organizations can strengthen their risk management strategies and create a resilient defense against cyber threats.
In conclusion, effective risk management is critical for organizations seeking to proactively identify, assess, and reduce cybersecurity threats. When businesses integrate cybersecurity compliance into their risk management frameworks, they create a comprehensive approach to safeguarding sensitive data. Given the evolving nature of cyber threats, prioritizing risk management will be important for long-term security and success for any business.
Key Regulatory Compliance Requirements for Modern Businesses
Regulatory compliance has become an essential component of protecting corporate integrity, as it ensures that businesses safeguard private information and uphold customers’ right to remain anonymous by adhering to industry and regional regulatory frameworks.
Each region and industry also has its own set of regulations; therefore, each company needs to be aware of what those regulations entail to protect itself from possible risks.
One of the most significant regulations influencing other countries is the GDPR. This regulation imposes a strict standard on how all organizations collect and manage personal information throughout the European Union.
The CCPA is currently one of the strongest consumer data privacy laws in the United States. As with many state-level laws that provide consumers with additional rights related to their personal identifiable information, many states are developing their own laws.
The main compliance standards (requirements) that most companies will typically follow include:
- Protection of personal data/privacy of customers
- Correct management of company information
- A timely response to breaches of security
Companies that comply with these regulatory requirements protect themselves from heavy penalties. In addition, by being compliant with regulatory requirements, you build trust with your clients. The way you manage and process client data is transparent and trusted.
However, managing these regulatory compliance issues can be an issue for many organizations. Companies want to ensure that all regulatory compliance requirements align with their operational goals so they can successfully integrate them into their operations.
It is important to stay current. Compliance regulations are always changing. They are evolving as new threats and technological developments emerge.
Regulatory compliance is about much more than just checking boxes. Regulatory compliance is an ongoing effort to protect both your organization and your clients.

Markus Winkler (https://unsplash.com/@markuswinkler)
As companies take a proactive approach toward implementing and maintaining effective compliance programs, they will be able to outdo their competitors. The investment in an ethical, compliant business model also demonstrates the company’s ability to protect its customers’ information.
Cybersecurity Compliance Frameworks Comparison

Insight: Businesses often follow multiple frameworks simultaneously, depending on industry and location
Source:
- NIST Cybersecurity Framework
https://www.nist.gov - ISO Standards
https://www.iso.org
Cybersecurity Compliance Trends: Cybersecurity compliance trends highlight how modern businesses adapt to evolving threats and regulations.

Using cybersecurity compliance trends to establish a strategy that modern organizations use to secure their data while adhering to various regulatory requirements is vital to developing an effective cybersecurity program. Modern organizations must recognize the rapid growth of digital technology and continually assess emerging cyber threats and regulatory changes related to data protection and cybersecurity. Cybersecurity compliance trends help organizations assess and mitigate the risk of non-compliance while enhancing their overall security posture.
The two largest areas of cybersecurity compliance trends are data privacy laws and technology. Due to legislation passed into law, including the GDPR, CCPA, etc., there have been stringent requirements placed on organizations collecting and storing personal identifiable information. As these laws continue to evolve, organizations must remain flexible and responsive to the regulatory landscape, adapting their cybersecurity compliance frameworks to maintain ongoing compliance. Organizations are beginning to recognize the importance of cybersecurity compliance as a core component for any organization operating in current regulatory environments.
In addition to the growing awareness of the importance of data privacy laws, another cybersecurity compliance trend is the increased adoption of advanced technologies. Artificial Intelligence (AI), Machine Learning (ML), and related technologies are being used by organizations at an increasing rate to support their compliance activities. AI and ML enable organizations to analyze large volumes of data, identify potential vulnerabilities, and streamline compliance processes. Organizations using these technologies can enhance their cybersecurity compliance posture while identifying and mitigating potential future threats.
Cybersecurity Compliance Trends Indicate a Shift Toward Collaboration. Organizations have realized that they need to involve more than just one department in all cybersecurity compliance efforts. A collaborative approach to cybersecurity compliance fosters a culture of general security awareness throughout the organization. With increased awareness of cybersecurity compliance, companies can protect themselves from the negative financial impact (e.g., fines) and reputational loss associated with noncompliance.
The rapid adoption of Remote Work/Hybrid Models by many companies has dramatically changed how business organizations address cybersecurity compliance. Many organizations have adopted flexible yet secure methods to protect company data when accessed remotely. These changes have required most companies to implement a wide range of comprehensive cybersecurity compliance programs, including protections for remote access and device management, ultimately protecting sensitive company data wherever employees access or create it.
Cybersecurity Compliance Trends provide organizations with the critical information needed to adapt to evolving threats and regulations. Organizations that leverage these trends will improve their cybersecurity compliance frameworks, integrate emerging technologies into their current cybersecurity practices, and foster a culture of awareness among their team members. The rapidly evolving nature of cyber threats will require organizations to stay up to date with the latest cybersecurity compliance trends to maintain ongoing protection and customer trust in today’s increasingly complex digital world.
Top Cybersecurity Compliance Trends Shaping 2024 and Beyond
Cybersecurity compliance regulations are ever-changing due to increasing threat levels and changing technology trends. Staying current with trends will be necessary if companies want to remain competitive.
The most obvious area where we see this trend is with the emergence of cloud security. As more and more data moves into the cloud, it is imperative that we protect this information. Companies are therefore implementing various cloud-based compliance protocols to minimize the risk of storing large amounts of sensitive information in a single location.
Another area that has created an issue, as a result of the ongoing pandemic, is remote/hybrid work environments. Securing remote or hybrid work networks is critical; thus, organizations must update their cybersecurity frameworks to account for increased exposure to cyber threats.
A final trend is the use of Artificial Intelligence (AI) and Machine Learning (ML), which can help detect potential cyber threats. AI/ML allows companies to gain real-time insight to better anticipate future cyber threats.
Key trends include:
- Cloud security protocols are increasingly important to businesses.
- Businesses must adapt their cloud-based security to meet the needs of remote workers.
- Artificial intelligence (AI) and machine learning (ML) are increasingly used in threat management.
- Data privacy regulations are becoming much more of a focus for businesses.
A Chosen Soul (https://unsplash.com/@a_chosensoul)
In addition to investments in cybersecurity resilience, businesses are establishing robust incident response plans to enable rapid responses to potential cyber threats.
Cybersecurity is increasingly being integrated into all aspects of a company’s strategic direction. A company that takes this holistic approach can ensure its compliance initiatives align with its overall business objectives.
By understanding these key trends, companies can protect themselves while creating opportunities to be recognized as industry leaders in cybersecurity. Companies that develop flexible, responsive approaches to future challenges will ultimately create an environment that positions them competitively for regulatory compliance.
Essential Risk Management Strategies for Compliance
Cybersecurity compliance through effective risk management is paramount in today’s business environment. Companies need to develop and implement an effective strategy to both identify and manage cyber-risks.
An assessment of potential cyber risk (a.k.a. a risk assessment) is fundamental to any successful cybersecurity plan. The process will allow companies to identify their weaknesses and, therefore, take targeted, relevant action based on the results.
After identifying potential cyber-risk(s), they must be evaluated. Companies should utilize available resources to mitigate the highest priority cyber-risk(s) first. Focused effort will lead to improved company-wide cybersecurity postures.
Multi-layered security solutions can greatly reduce the risk associated with an individual threat. Multi-factor authentication and encryption technologies can also provide enhanced protection for sensitive information.
Security audits should be conducted regularly by businesses. Compliance with evolving regulations will be easier to achieve, and identifying areas that require additional attention will also be facilitated.
Key elements of an effective Risk Management Strategy include:
- Regularly conducting risk assessment
- Prioritize your Risk Management strategy
- Implement Encryption/Authentication technology to secure data
- Perform regular Security Audits
Zulfugar Karimov (https://unsplash.com/@zulfugarkarimov)
The ability to work collaboratively with other organizations is a key element in achieving success in Risk Management. Working with external consultants or third-party professionals will help identify potential risks that may have been missed internally and enhance the effectiveness of any internal risk management strategies you employ.
Providing employee education is another important aspect of successful risk management. Providing employees with information on how to manage their own risk (i.e., following security best practices) will strengthen your company’s overall defensive posture.
Proactive Risk Management is essential when navigating today’s threats. By combining these strategies into your Risk Management plan, companies can meet their compliance obligations as efficiently as possible. A proactive approach to managing risk not only supports a company’s regulatory compliance obligations but also creates a positive perception among its stakeholders and customers.
Risk Management Process
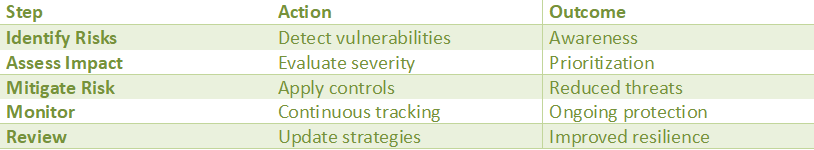
Example: A company identifies phishing risk-trains employees-reduces breach likelihood.
Source:
- NIST Risk Management Framework
https://www.nist.gov
Building a Future-Ready Cybersecurity Framework
Modern Cybersecurity Frameworks are needed by modern businesses. Because of evolving cyber threats, they must be able to respond rapidly to new or emerging ones.
Compliance needs to be integrated into the framework’s structure. Compliance will enable organizations to maintain alignment with regulatory requirements while implementing new security measures.
Organizations need to implement a comprehensive cybersecurity framework. Examples of these are NIST and ISO 27001. They provide a well-defined set of guidelines and standards for compliance.
Continuous monitoring is another essential element of this process. Continuous Monitoring enables organizations to detect and identify threats on a “real time” basis and enables them to respond quickly to incidents, thereby limiting potential damage.
Finally, organizations need to invest in cutting-edge technologies, including artificial intelligence (AI) and machine learning, to support automated threat detection, vulnerability identification, and data-driven decision support, improving their overall security posture.
A “future-proof” cybersecurity framework includes:
- A Regulatory Compliance Framework (the above-referenced framework) will address the integration of regulatory compliance for the company as it relates to Cybersecurity
- The adoption of NIST and/or ISO 27001 Guidelines
- Ongoing Threat Monitoring
- The use of Artificial Intelligence (AI) and Machine Learning (ML)

Zheng Yang (https://unsplash.com/@zyangdev)
In addition to being adaptable and resilient, a “future-proof” cybersecurity framework requires collaboration among organizational departments. When all departments work together, they will ensure that the overall Security Strategy developed by IT is well-rounded and Inclusive.
A leader’s ability to implement a “Future-Ready” Cybersecurity framework is critical.
Leadership will drive the development of the company’s Cybersecurity Strategy and foster a culture of security across the organization.
Therefore, if a business adopts the practices outlined above, it will have created a “future-ready” Cybersecurity framework that will protect its Data and Reputation and ensure ongoing compliance with changing laws and regulations.
The Role of Technology: AI, Automation, and Emerging Tools
In addition to providing significant benefits to business operations, technology is leading the way in helping organizations comply with emerging cybersecurity trends.
Specifically, AI and automation will completely transform how companies manage cyber threats.
Using AI will enable organizations to detect and respond to potential threats much faster. By analyzing large amounts of data using machine learning algorithms, organizations can identify new threat patterns and predict when a security incident may occur.
By automating routine tasks, organizations can allow their information security staff to concentrate on larger-scale strategic planning and policy development. Organizations also benefit from relying on a consistent automated process rather than inconsistent manual effort and errors in high-risk areas.
New types of products and services are becoming available as well, specifically threat intelligence platforms that help organizations understand the types of threats they face today. Threat intelligence platforms collect and analyze information from multiple sources to give an organization a clear understanding of the current threat environment.
Organizations have no choice but to use this technology to meet ever-changing regulatory requirements and maintain compliance in securing their IT assets.
Businesses will experience numerous benefits by incorporating artificial intelligence (AI), automation, and emerging tools into their security programs. These include:
- Improved speed for identifying and responding to threats
- Lowered operational expenses and improved efficiency
- Enhanced capacity to anticipate future attacks
- More accurate assessments of the types of threats a business is likely to face

by Julio Lopez (https://unsplash.com/@juliolopez)
In addition to mitigating the drawbacks of adopting new technology, businesses must remain aware of emerging trends and developments. As such, the continued development of security measures will help to maintain a strong position.
The use of AI, automation, and related technologies will enable organizations to proactively identify and address potential vulnerabilities before they develop into actual problems.
By embracing new innovations, businesses can ensure their operations align with existing and anticipated regulatory and compliance mandates. Through this alignment, businesses will ultimately achieve long-term sustainability in an evolving threat environment.
AI & Automation in Cybersecurity
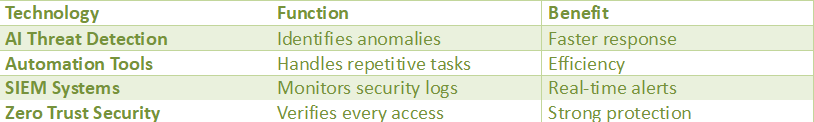
Insight: AI-driven tools are becoming essential for real-time compliance and threat detection.
Source:
- Microsoft Security
https://www.microsoft.com/security - IBM Security
https://www.ibm.com/security
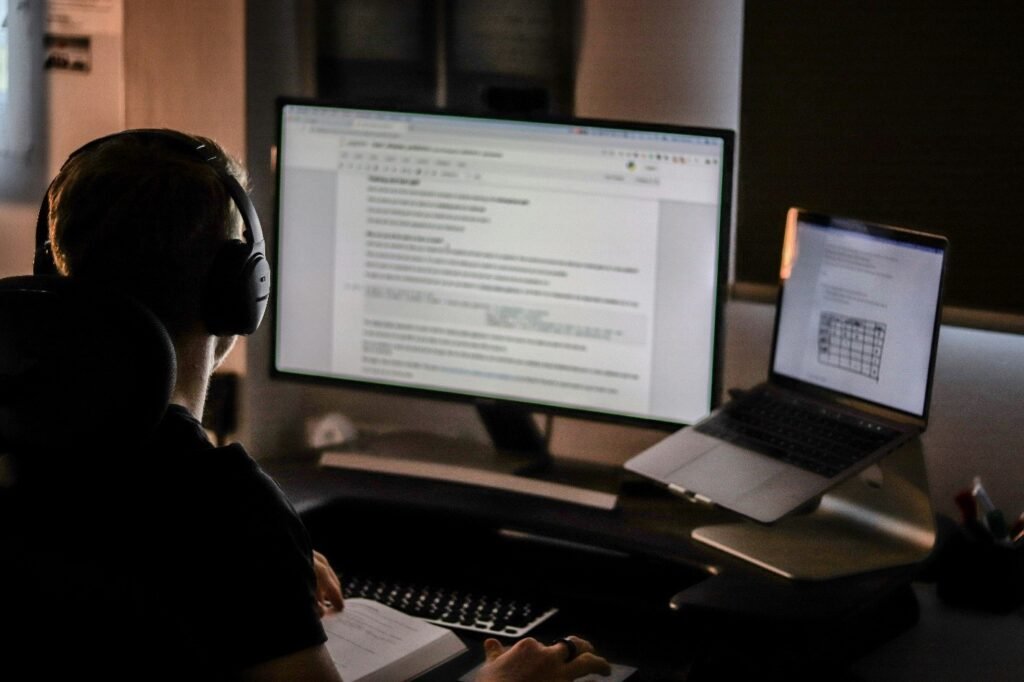
Addressing Compliance Challenges in Remote and Hybrid Work Environments
The remote and hybrid work environment creates different regulatory compliance issues for businesses than the traditional office setting.
It introduces additional vulnerabilities (i.e., an expanded “attack surface”) by distributing company data across multiple locations.
A new method must be used to secure the company’s dispersed data. A business must verify that each remote device is secured at the same level as, or at a higher level than, its on-site counterparts.
Remote access is typically done through a user’s home network. Home networks are often less protected than corporate networks; therefore, they provide potential entry points for malicious activity.
Businesses will have to implement strict policies and controls on employee use of personal devices, in addition to managing the growing number of employees working remotely.
Key strategies to address these challenges are:
- Implement virtual private networks (VPNs), so remote workers can have safe access.
- Take a Your Own Device (BYOD) policy seriously, with enforceable rules.
- Frequently provide remote workers with security training.
by Samuel Bourke (https://unsplash.com/@sambourke)
Protecting the cloud is also important because many businesses use cloud services for collaboration. To protect data in these cloud environments, strong security measures are required.
Regular auditing of security practices in remote workplaces helps identify vulnerabilities. Staying vigilant will help companies stay ahead of new threats.
Compliance has never been just about following policy in this remote era. Compliance is creating a culture that prioritizes trust and security at all locations.
Remote Work Compliance Challenges
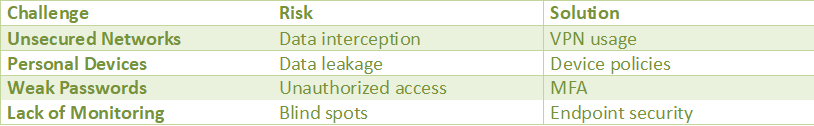
Key Insight: Remote work increases attack surfaces, requiring stronger compliance controls.
Source:
- Cisco Cybersecurity Report
https://www.cisco.com - Deloitte Cyber Trends
https://www2.deloitte.com
Industry-Specific Compliance Considerations
Compliance can vary significantly across business sectors. The reasons for this are primarily differences in regulatory standards and business operations.
Healthcare is subject to specific regulatory guidelines under HIPAA. Healthcare providers have a legal obligation to protect sensitive personal health information.
In contrast, Financial Services is subject to laws governing how it handles customers’ confidential financial information. These include, but are not limited to, Gramm-Leach-Bliley (GLBA).
Finally, retailers must also comply with regulatory guidelines and industry standards, including those that provide safe handling practices for consumers’ credit card information.
Key factors that are often particular to an individual sector or industry include:
• Electronic Health Records (EHRs) in Healthcare.
• Securing Financial Transactions in Finance.
• Customer Payment Information in Retail.

by lonely blue (https://unsplash.com/@lonelyblue)
Identifying specific regulatory compliance requirements is also important, as each industry will have different compliance strategies based on its own needs.
A company failing to follow industry guidelines may be subject to heavy fines. In addition, companies found to be out of compliance may lose customer trust and damage their reputation.
In heavily regulated industries, it is imperative to remain current on regulatory trends. A proactive strategy is key to identifying new threats before they become major issues.
Developing a company’s Cybersecurity Strategy based on an Industry-specific Compliance Regulatory Environment will improve your organization’s overall Security Posture. This will help you reduce risk and sustain Business Operational Resilience.
Advanced & Secure HIPAA Cybersecurity for Healthcare Organizations
Best Practices for Ongoing Compliance and Continuous Improvement
Ongoing activities are necessary to sustain cybersecurity compliance. To stay ahead of evolving threats and keep up with changing regulations, businesses will need to be in “improvement” mode at all times.
Regular auditing is a means by which companies can maintain their compliance posture. Audits help identify vulnerabilities and potential improvements. Audits also provide assurance that the company is maintaining current levels of protection through ongoing review of the security controls in place.
Employee training is another significant activity related to maintaining compliance. Employees need to have knowledge of the applicable compliance requirements as well as knowledge of recent/emerging threat types. This enables employees to take proactive steps to protect against security incidents.

by Beatriz Cattel (https://unsplash.com/@bicattel)
Companies may use automated/compliance tools to make the compliance process easier and faster. Automated tools enable real-time monitoring and can alert you to discrepancies.
For continued effectiveness of ongoing compliance, the organization may wish to implement a number of strategies, including:
- Periodic (routine) security audit and risk assessment
- Continued or periodic employee training on compliance issues
- Cybersecurity compliance automation
- Frequent review and update of cybersecurity policy
All of the above provide a basis for building an organization-wide compliance program that will serve as the foundation for anticipating, identifying, and addressing emerging cyber threats over time.
Additionally, developing a compliance-based culture within your organization will be critical to sustaining a long-term cybersecurity posture.
Conclusion: Staying Ahead in Cybersecurity Compliance
The journey to remain compliant with evolving cyber laws and continually changing security threats is one that organizations will have to continue. A business today needs to be vigilant to successfully adapt to regulatory changes and new threats. The most effective way for companies to succeed is to adopt a proactive approach to compliance and continuously monitor for breaches.
Companies need to use technology to support their compliance efforts. Organizations that leverage artificial intelligence (AI) and automation will find these technologies beneficial for streamlining many complex compliance tasks and protecting sensitive information. By utilizing both AI/automation technologies and human knowledge/compliance professionals, an organization will achieve a strong level of protection.
Cybersecurity compliance, like all other areas of compliance, is a multifaceted effort. Compliance efforts require coordination among departmental groups within an organization; however, by adhering to best practices and fostering a culture of innovation and continuous improvement, an organization will be confident in its ability to successfully address cybersecurity compliance issues over the years.
FAQs
Question: What are cybersecurity compliance trends?
Answer: Cybersecurity compliance refers to the ways in which companies continually develop and adapt their practices and procedures to comply with regulatory standards in order to protect sensitive company information from unauthorized access, theft, or damage.
Cybersecurity compliance is a dynamic process; each time there is a new type of cyberattack or a regulatory body issues a new set of rules governing how businesses must collect, store, use, and discard customer and employee information, businesses will need to develop new strategies to protect this data and/or update existing ones.
Question: Why is cybersecurity compliance important for businesses?
Answer: There are several reasons why cybersecurity compliance is important. Protecting sensitive data from being stolen by hackers is one reason. Companies may be fined by regulatory agencies if they do not follow all applicable laws. Companies that fail to follow established compliance guidelines lose customers to those that do.
Following established compliance guidelines means that companies put into place appropriate security measures designed to minimize risk when dealing with potential cyber threats. Ultimately, companies have greater confidence in their ability to prevent cyberattacks and respond appropriately if an attack occurs when they follow established compliance guidelines.
Question: How do data privacy regulations like GDPR impact cybersecurity compliance?
Answer: The European Union’s General Data Protection Regulation (GDPR), enacted in 2018, has imposed stricter restrictions on how organizations handle customer and employee personally identifiable information. Organizations subject to GDPR requirements must implement specific security measures to protect this personally identifiable information. Furthermore, organizations subject to GDPR requirements must conduct periodic audits of the controls implemented to protect personally identifiable information.
Finally, organizations subject to GDPR requirements must establish clear policies regarding how personally identifiable information collected from individuals will be used. Organizations must continue to evolve their approach to compliance as regulatory requirements change.
Question: What role do advanced technologies play in cybersecurity compliance trends?
Answer: Technologies such as Artificial Intelligence (AI) and Machine Learning (ML) have played a major role in advancing cybersecurity compliance. These technologies allow organizations to automatically manage compliance tasks. They enable organizations to review vast amounts of data for possible vulnerabilities and provide real-time threat detection. The integration of AI and ML enables organizations to strengthen their cybersecurity capabilities and rapidly adapt to new compliance requirements.
Question: How can organizations foster a culture of cybersecurity compliance?
Answer: A number of methods exist for fostering an organizational culture of cybersecurity compliance. One method involves educating employees at various levels within an organization about the elements of good security practice. Another way is to involve personnel from multiple departments in your compliance efforts. A third element is to promote open communication throughout your organization about how you are protecting yourself against cyber threats.
When all members of an organization understand the value of cybersecurity compliance, the risk of an adverse event occurring is minimized, and the likelihood of meeting applicable regulatory requirements increases.