The employees log in to the patient scheduling program, and at 8:00 am Monday morning, the employees at the front desk are in for a shock. “Your files are encrypted,” reads the message across the screen. All phone calls to reach patients are unsuccessful, and there are no scheduled appointments for the remainder of the month.
While it may seem like something from the movies, unfortunately, this is an example of one of the many unfortunate digital disasters that occur when practice managers believe that they are providing all of the necessary protections to ensure the confidentiality of their patients’ private information and are unaware of or disregard the HIPAA Security Rule, which provides direction to HIPAA compliant practices regarding security of protected health information online; however, it is here that nearly all large scale (expensive) breaches of protected health information occur.
As mentioned above, the financial consequences of a large-scale breach of protected health information are also extremely high. According to IBM’s “Cost of a Data Breach Report,” the average cost of a large-scale data breach involving protected health information has now exceeded $10 million. In addition, a “digital shutdown” represents a risk to patient safety. If clinics are forced to cancel surgical and/or medical procedures due to a breach and if hospitals are required to redirect emergency ambulances, then effective data breach prevention in healthcare is critical to delivering quality patient care.
This Guide was developed to assist Practice Managers, Clinicians, and Administrators in protecting themselves and their organizations against cyberattacks by explaining and clarifying how to implement HIPAA Cybersecurity. With this Guide, you will find examples of questions to ask your IT vendors to help you become a strong advocate for yourself, your organization, and, most importantly, your patients.
Summary
“HIPAA Cybersecurity for Healthcare Organizations—Why Privacy Training Is Not Enough” explains why HIPAA Privacy Training alone will not be enough to protect your organization’s EPHI in this new age of threats. The article describes a ransomware attack in detail to show how quickly a cyber incident can turn into a full-blown patient safety and business continuity disaster, resulting in millions of dollars in costs and disruption of care services due to the breach(s).
It also presents simple, non-technical descriptions of effective strategies for defending your organization’s EPHI that healthcare executives can advocate for, even if they lack technical expertise. Some of these are Multi-Factor Authentication (MFA), which is probably one of the best defenses against account takeover attacks. It shows how encrypting data results in a HIPAA “Safe Harbor”, essentially making a loss/stolen device with encrypted information no longer a breach.
Additionally, the article advocates for the concept of a “Human Firewall”, pointing out that annual training sessions are not sufficient to create awareness in staff members. Therefore, it encourages ongoing, simulated phishing exercises that mirror those encountered in everyday life.
Beyond standard Antivirus Software, it recommends using Modern Endpoint Protection (EDR) to monitor ransomware behavior and stop such attacks before too much of your network is encrypted. Lastly, the article discusses Third Party Risk Management. While BAAs (Business Associate Agreement) are mandated under HIPAA regulations, it notes that they are merely a starting point. It recommends that all organizations regularly audit their vendors and ask them security-related questions during the vetting process.
HIPAA cybersecurity: HIPAA cybersecurity helps healthcare organizations protect sensitive patient data and ensure compliance with privacy and security regulations

HIPAA cybersecurity helps healthcare organizations protect sensitive patient information and ensure compliance with applicable privacy and security regulations. HIPAA cybersecurity is more than just being HIPAA compliant; it addresses real cyber threats such as ransomware, phishing, insider abuse, lost/stolen devices, and accidental disclosure of ePHI that may adversely affect patient care and safety.
Protecting Electronic Protected Health Information (ePHI), wherever it resides — including in electronic health records (EHRs), billing software, patient portal applications, email systems, backup tape media, cloud storage solutions, and connected medical equipment — is the primary function of a HIPAA cybersecurity program.
A HIPAA cybersecurity program starts by determining what type(s) of ePHI an organization maintains, what the organization does with its ePHI, who has access to its ePHI, and what happens if something were to go wrong. This is why completing a risk assessment and managing identified risks on a routine basis are so important for complying with the Security Rule’s HIPAA standards.
The goal of HIPAA cybersecurity programs is to implement practical measures to reduce the probability and impact of a cyber-incident to comply with the Security Rule’s standards.
The most common “building blocks” for this purpose include: (i) establish appropriate access controls (e.g., unique user IDs, role-based access rights, removal of access rights once they are no longer required), (ii) use multi-factor authentication, (iii) encrypt all forms of ePHI at-rest and in-transit, (iv) maintain current configuration settings and apply all available patches, and (v) monitor and audit logs related to potentially malicious activities as soon as reasonably possible. Reliably backing up ePHI, protecting those backups against unauthorized changes, and having the capability to restore the backed-up information are other significant aspects of a HIPAA cybersecurity program.
To have an effective HIPAA cybersecurity program, an organization must implement administrative, physical, and technical safeguards. Examples of these include: (i) workforce training to educate employees on HIPAA and cyber-threats, (ii) creation of policies and procedures that will provide direction for employees regarding how to appropriately handle sensitive information, (iii) vendor oversight to assure business associates are meeting their contracted obligations, and (iv) development of incident response plans to allow organizations to quickly respond to potential breaches.
When you create contracts with your business associates, it is very important to establish clear expectations regarding the respective security obligations of both the organization and the business associate. In addition to establishing the obligations and duties of both parties, the organization must verify that its business associates comply with the terms of the agreement (contract).
The education and training of your employees can significantly reduce the amount of Human Error that occurs day to day. The education/training should focus on the different ways an employee can be deceived through phishing, how to manage ePHI appropriately, and how to quickly report any potential breaches or other issues concerning ePHI.
Day-to-Day HIPAA Cybersecurity Processes will be successful when Security is built into Clinical Workflows, rather than introduced as an additional barrier to the delivery of Patient Care. Examples of simple actions to take include: replacing texting with secure messaging, turning off screens automatically after a period of inactivity, and providing least-privilege access to all users.
Tabletop Exercises and Incident Response Drills conducted regularly will also help organizations determine whether their team(s) can provide rapid response and resolution during a suspected data breach.
In summary, HIPAA Cybersecurity represents an ongoing process of Risk Mitigation, Responsibility, and Readiness intended to protect patients, build trust, and assist healthcare organizations in complying with regulatory requirements for ongoing compliance.
#Complete & Secure SOC 2 Compliance Checklist for Data Security
The Two Sides of HIPAA: Why a Locked File Cabinet Isn’t Enough Anymore
HIPAA Privacy Rule
Every healthcare provider understands the HIPAA Privacy Rule. You understand why you can’t leave a patient’s medical record lying around, and why you can’t talk about a patient’s case at a coffee shop. The HIPAA Privacy Rule establishes both the rights of individuals involved in handling protected health information and the circumstances under which someone may access that information.
With the modern digitalization of patient records, there is another aspect to HIPAA. Almost all of today’s largest dollar HIPAA violations are committed electronically. They are either committed by hackers who gain access to your computers and/or servers, or by simply sending a patient’s identifiable information via email.
HIPAA Security Rule
The HIPAA Security Rule addresses this issue by defining what constitutes the protection of Electronic Protected Health Information (ePHI). It states that ePHI cannot be accessed without authorization. If an individual gains unauthorized access to ePHI (via hacking), or if the information is sent via email unintentionally (sending confidential patient information via email), the HIPAA Security Rule addresses this issue. The HIPAA Privacy Rule represents your data protection policy.
The HIPAA Security Rule is your digital alarm system and your safe. This rule sets forth specific technological standards for securing ePHI, recognizing that relying on physical means alone (i.e., a “paper-based” process) to secure patient records is insufficient.
If you have developed the very best data protection policies for your practice, but fail to establish the required technological protections to safeguard those policies, then your failure to establish such protections will directly constitute a HIPAA Cybersecurity violation. For example, even if you lock up your file cabinets, a ransomware virus that disables every computer in your office will accomplish little more than putting your patients’ confidentiality at risk. Therefore, establishing a comprehensive electronic protection strategy will provide both you and your patients with greater safety and confidence.
HIPAA security rules: Learn how HIPAA security rules protect sensitive healthcare data from cyber threats
HIPAA Cybersecurity also uses the HIPAA Security Rule’s structure but applies it in a more practical way, using defense strategies for organizations of different sizes, across all systems, and at varying degrees of risk. A significant part of the HIPAA Security Rule involves conducting an accurate and comprehensive risk assessment, then implementing appropriate risk mitigation measures to address vulnerabilities.
Therefore, a practical HIPAA Cybersecurity program begins with the same process: identify where ePHI is stored and transmitted (EHRs, billing applications, email, backups, mobile devices, vendors), identify potential threats to ePHI, and prioritize corrective actions. In addition to emphasizing Administrative Safeguards such as developing security policies, providing worker education and training, and establishing incident response plans — since attackers have accessed sensitive data most frequently via employee actions — the HIPAA Security Rules.
Therefore, a practical HIPAA Cybersecurity Program starts off with this same process:
Identify where ePHI is being stored and/or transmitted (for example: Electronic Medical Records/Electronic Health Records, Billing Application(s), Emails, Backup Data, Mobile Devices, Vendor’s Systems);
Identify possible threats to your organization’s ePHI.
Prioritize corrective actions.
In addition to the emphasis on Administrative Safeguards such as creating and maintaining organizational security policies, educating/training workers, and planning for incidents involving sensitive data — since hackers have most commonly gained unauthorized access to sensitive data via employees — the HIPAA Security Rules.
HIPAA Security Rules Technical Safeguards — Next up in this review will be Technical Safeguards. Technical Safeguards include access controls (unique User IDs, Role-Based permissions, and auto-logoff), audit controls (logging/review of activity), integrity controls (preventing improper alteration/destruction of ePHI), and transmission security (protecting data in transit). Implementing strong authentication practices like multi-factor authentication, timely patching, secure configurations, and encryption when needed makes it much harder for hackers to navigate a network or access data.
When organizations implement the HIPAA Cybersecurity Rule, they need to create a repeatable process: On/Off-boarding Access, Regularly conducting vulnerability scanning, device management, securely backing up data, recovery testing, business associates, and vendors are also very important since vendor oversight, contracts, and verification are vital since third parties handle ePHI. To identify suspicious behavior early and reduce impact, continuously monitor HIPAA Cybersecurity and inform your team of potential threats.
Implementing the HIPAA Security Rules allows organizations to protect sensitive healthcare information, ensure continuity of care, and provide evidence of compliance during audits/investigations by utilizing HIPAA cybersecurity practices. Additionally, by remaining current with HIPAA Security Rules and continually enhancing controls, organizations can stay aligned with evolving cyber threats and modern healthcare operations.
HIPAA Security Rule Safeguards
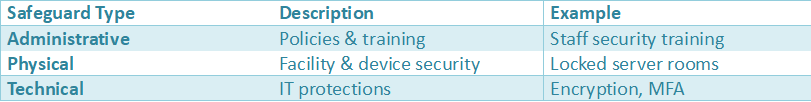
Insight: HIPAA security is built on three pillars – administrative, physical, and technical safeguards.
Source:
- U.S. Department of Health & Human Services (HHS)
https://www.hhs.gov/hipaa
HIPAA cybersecurity requirements: Understand the essential HIPAA cybersecurity requirements for safeguarding patient information

Beginning HIPAA Cybersecurity Requirements With the HIPAA Security Rule:
The HIPAA Security Rule was developed to establish standards for organizations to protect Electronic Protected Health Information (EPHI) against “reasonably anticipated” cyberattacks and other breaches. The primary goal of the Security Rule is to minimize the occurrence of unauthorized access to EPHI, disruption in the delivery of patient care, and/or loss of patient information.
Additionally, the HIPAA Cybersecurity Rule provides each covered entity with the flexibility to choose those types of administrative, technical, and physical safeguards most applicable to their specific business model, regardless of whether they are large or small; whether they are using cloud applications or traditional systems; or how much risk is associated with protecting their EPHI.
There are two basic components to HIPAA Cybersecurity Requirements. First,
- Performing a complete and adequate Risk Analysis. A Risk Analysis involves identifying where EPHI is created, used, and transferred throughout your organization (i.e., electronic health records, billing systems, email, cloud-based applications, laptops/tablets/smartphones, and backup processes). Second, you need to assess the potential risks to EPHI in your organization, such as phishing, ransomware attacks, configuration errors, and insider misuse. Once you have identified potential risks to your EPHI, you must take action to manage them by implementing Risk Management activities. In doing so, this will allow you to determine the order in which you address the identified risks, identify who is responsible for addressing them, and track the status of your efforts.
- HIPAA Cybersecurity Requirements include Administrative Safeguards. Organizations must create and update as necessary their own policies and procedures related to security; provide annual training on security-related topics to all employees; establish disciplinary action for any employee(s) violating an organization’s policy governing access to and use of EPHI; and develop and maintain a written incident response plan that describes steps for reporting incidents; containing any damage caused by an incident; investigating any incidents; and notifying federal or state authorities when there is an unauthorized disclosure of EPHI.
Technical Safeguards are another critical component of HIPAA cybersecurity requirements. Administrative, Technical Safeguards (access controls) require a combination of secure user IDs and role-based access permissions for users to log in to systems/networks. When an employee leaves the organization or is transferred to a different department within the same organization, their access must be removed.
Audit controls, including monitoring logs, will help identify suspicious behavior. Integrity controls provide assurance that electronic protected health information (ePHI) has not been improperly modified/destroyed and that transmission security was used to reduce risk when moving ePHI over networks. As needed, additional layers of security may be added through encryption and multi-factor authentication, especially for remote access and cloud services.
Physical safeguards are also part of HIPAA cybersecurity requirements. Physical safeguards include the physical security of devices/workstations, facility access control procedures, and an organization’s policy on mobile device use/media disposal. Additionally, all critical ephi must have a secure backup plan. The backups must be protected against unauthorized access/tampering; they must also be tested regularly to ensure availability and recovery in the event of a system failure/ransomware attack.
Finally, HIPAA cybersecurity requirements apply to vendors/partners. Organizations must obtain business associate agreements from their third-party vendors and assess whether those vendors are using reasonable safeguards to protect ePHI. Lastly, ongoing documentation ensures that safeguards are implemented, monitored, and continuously enhanced over time.
Healthcare Cyberattack Statistics
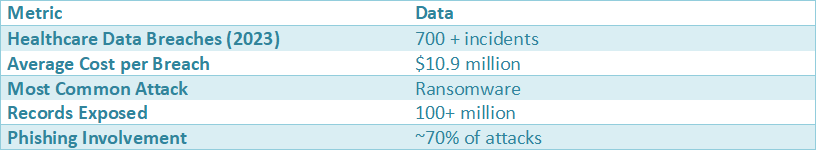
Key Insight: Healthcare is the most targeted industry for cyberattacks.
Source:
- IBM Cost of Data Breach Report
https://www.ibm.com/security - HHS Breach Portal
https://ocrportal.hhs.gov
HIPAA compliance cybersecurity: Discover how HIPAA compliance cybersecurity helps healthcare organizations meet regulatory standards

The terms HIPAA Compliance and HIPAA Cybersecurity refer to how Healthcare Organizations (HCOs) interpret their HIPAA obligations as they relate to the everyday protection of Electronic Protected Health Information (ePHI), through a combination of policies, processes, and technology. By using HIPAA Compliance Cybersecurity in this way, HCOs may see fewer breaches due to an organization’s failure to establish adequate controls to protect its ePHI. When performed effectively, HIPAA Compliance Cybersecurity builds trust with patients regarding their use of their ePHI and allows Clinical Operations to operate uninterrupted.
HIPAA Compliance Cybersecurity involves identifying all storage locations and methods used to store or transport ePHI, including EHR systems, Billing Platforms, Email, Cloud Applications, Endpoints, Backup Systems, and Third-Party Services. The initial steps toward implementing HIPAA Compliance Cybersecurity are the performance of a documented Risk Analysis, followed by the development of a Risk Management Plan.
The Risk Management Plan identifies, prioritizes, assigns ownership, and tracks the completion of remediation for each identified Risk. Therefore, compliance with HIPAA Cybersecurity becomes measurable once identified Risks have been mitigated through the establishment of Controls, the tracking of these Controls, and the measurement of progress.
In addition to developing a document-based Risk Assessment and Risk Management Plan, HIPAA Compliance Cybersecurity also enables Teams within an Organization to align on enforceable administrative safeguards for protecting ePHI. These include: Written Security Policies, Employee Training, Sanction Policies for Unauthorized Access and Documented Procedures for Adding/Removing Access to Sensitive Data.
HIPAA Cybersecurity enhances an organization’s readiness to address incidents by developing incident response plans and escalation procedures; providing a forum for simulated exercises using tabletop training; and developing procedures to investigate suspected privacy breaches. Additionally, a mature HIPAA compliant cybersecurity program educates employees on what constitutes a phishing attempt, which employee behaviors may indicate suspicious activity, and how to appropriately protect sensitive information (ePHI) at each step of handling ePHI.
Technical Controls of HIPAA Compliance Cybersecurity. A component of technical controls in HIPAA-compliant cybersecurity is Role-Based Access Control (RBAC). RBAC allows users access based upon their job functions. Users can then obtain unique User IDs that allow tracking of who accesses specific parts of an organization’s electronic protected health information (EPHI).
Multi-Factor Authentication (MFA) ensures no single person has multiple ways into an organization’s EPHI. Audit Logs provide rapid identification of possible problems/areas of concern in an organization’s cybersecurity and are used in conjunction with Regular Audits to detect potential breach(s)/vulnerabilities in an organization’s cybersecurity. The last element of technical controls for HIPAA compliance cybersecurity is the use of Encryption when sending/sharing EPHI between organizations.
Secure Data Exchange. An additional component of HIPAA compliance cybersecurity is Securely Exchanging Data. This is accomplished by either encrypting or securely transmitting EPHI. Examples of this include securely emailing EPHI or securely using Portals. The Final Element of HIPAA Compliance Cybersecurity. The final element of HIPAA-compliant cybersecurity is Implementing Best Practices in Patch Management, Securing Devices, and maintaining tested, resilient backups to reduce the impact of Ransomware Attacks. All three elements are important in applying HIPAA Cyber Security Practically to Protect an Organization’s EPHI.
Vendor Cybersecurity Management. Lastly, HIPAA compliance cybersecurity requires managing Vendors’ Cybersecurity through Business Associate Agreements (BAAs) and Ongoing Oversight. Organizations need to be able to confirm that their vendors implement Reasonable Safeguards to Protect the EPHI entrusted to them and that they clearly define their individual roles/responsibilities for protecting the organization’s EPHI. Periodic review/documentation of Vendors will assist organizations in demonstrating compliance with relevant HIPAA Cybersecurity Regulations and protect themselves from Emerging Cybersecurity Threats.
Your First Line of Defense: How Multi-Factor Authentication (MFA) Stops 99% of Account Attacks
For many years, there was a recommendation to create extremely long and complex passwords. While developing strong passwords is important, it does nothing to combat the growing trend of hackers using millions of stolen passwords obtained by breaching other sites to try to hack into systems containing your clinic’s sensitive information, such as email, patient scheduling, billing, and patient correspondence.
Implementing Multi-Factor Authentication (MFA), will be one of the best methods to reduce the risk associated with being able to utilize these stolen passwords to gain access to your clinic’s electronic protected health information (e-PHI). An example of how MFA works is as follows: when attempting to log in to your email, remote network, or EHR application, you enter your username and password.
Upon successful completion of this step, your IT department generates a one-time random number that will be displayed on your computer screen. At the same time, a corresponding random number will be generated and sent to your mobile phone via SMS/text messaging. Both numbers are then required to complete the authentication process. Therefore, if an individual steals your password, they will not have access to your email account, remote network, or EHR application, since they do not possess the second “physical” key.
Using MFA is considered one of the most effective means of protecting against unauthorized login attempts and can convert what would otherwise be an insecure method of accessing e-PHI into a secure entry point. The benefits of using MFA extend beyond protection against unauthorized access; according to Microsoft, whose leading researchers have studied various methods to reduce hacking risks, MFA has been shown to prevent more than 99% of account compromise attacks. Additionally, Microsoft’s research indicates that implementing MFA is the most effective measure taken thus far to meet HIPAA’s security requirements.

MFA Protection Impact
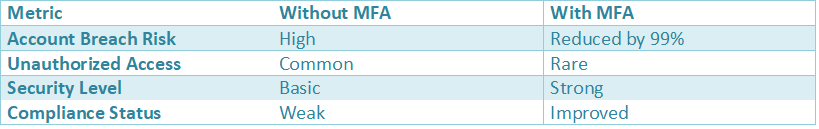
Example: organizations implementing MFA drastically reduce credential-based attacks.
Source:
- Microsoft Security Report
https://www.microsoft.com/security
The HIPAA “Safe Harbor”: How Encryption Turns a Disaster into a Non-Event
Encryption is the final layer of security protecting electronic protected health information (ePHI) and can protect your ePHI by making data unreadable unless the unauthorized user has the digital “key” to unlock the encrypted files. Think of encrypting a patient’s chart as writing the entire file in an unbreakable code. No matter how many attempts an unauthorized user makes to access the data on the laptop, it will always appear to them to be gibberish until they obtain the correct digital decryption key.
With proper encryption applied to data stored “at rest” on laptops, servers, and backup devices, you will receive an important “safe harbor” from being responsible for reporting and notifying patients of a potential data breach if your laptop containing ePHI is lost or stolen. Reporting and notifying patients is expensive, time-consuming, and usually results in unwanted media coverage. Additionally, it would result in your organization being listed on the HHS Public List of Breaches (“Wall of Shame”). It could help turn an otherwise disastrous situation involving a stolen device into something much less costly – just replace the stolen device.
You need to ensure that you are using encryption to protect your organization’s ePHI wherever possible. Proper endpoint security for healthcare devices requires that all laptops, servers, and backup drives store data in an encrypted format while the device is powered down or idle.
Your Human Firewall: Why Annual Training Fails and What to Do Instead
Now that you have encrypted your patient’s private data and locked down access using Multi-Factor Authentication, your attacker will now try to trick your employees. Studies indicate that 80% or more of cyber breaches are initiated when an employee is tricked into taking some action on behalf of the attacker, e.g., by clicking something they shouldn’t. Educating your healthcare staff on protecting their patients’ private health data from cyber threats creates the best protection for their private health data – your “Human Firewall.”
Unfortunately, most ways that organizations deliver education to their healthcare staff regarding defending against sophisticated cyber-attacks, which target healthcare-related data, via a single video or slide show presentation do not teach your staff the necessary skills required to successfully defend themselves against these types of cyber-threats. Even though education provided through a presentation may satisfy your regulatory compliance obligations, it does absolutely nothing to develop the practical world-reaction skill set needed to prevent a cyber-attack that results in the theft of sensitive healthcare-related information.
The methods used by attackers to deceive employees vary, but typically include sending emails purportedly from either an Employee Health Records Vendor or from a senior-level executive within your own organization. Today’s attackers use contemporary “Red Flags” that you should also teach your employees to recognize to prevent them from becoming victims of deception.
- Pressure to act immediately: Employees are being bombarded with emails that create a false sense of urgency (e.g., threats to shut down employees’ computers or demands for immediate payment).
- Mismatched senders: An email that appears to be from your IT department but does not include your company’s domain name in its sender information (helpdesk@secure-support.net).
- Links from malicious sites: Train employees to hover their mouse over a link before selecting it, and to check that the URL displayed in the browser window matches the link text.
The most effective method for developing the reaction skills necessary to rapidly identify the previously discussed red flags is continued phishing simulation. Simulation phishing is the sending of fake emails intended to resemble legitimate emails from trusted senders (e.g., your IT department) to your employees. When a simulated phishing attempt results in an employee falling victim to the scam, rather than the organization experiencing a real security incident, the employee receives an immediate, private educational session explaining that the email was fraudulent and specifically what actions the employee took.
Beyond Antivirus: How to Stop a Ransomware Attack in Its Tracks
The main point I want to make about handling a ransomware attack is to plan ahead. The best way to address this problem is through planning.
Although many people believe that their standard antivirus software will protect them from ransomware attacks, most antivirus programs act as security guards. In other words, they check the ID of anything trying to access their computer to see if it has been previously identified as something that should be blocked.
These types of security guards are very good at identifying and stopping known threats. However, there are so many new forms of ransomware appearing every single day that no matter what you use as a security guard to protect your computer(s), there is a high probability that one of these newer versions of ransomware will be able to bypass the security guard because it does not yet appear on its block list.
As such, using an Endpoint Detection and Response (EDR) program will enable better detection and response to new threats than the traditional use of an antivirus program. An EDR program works differently from a typical antivirus program. Instead of just looking for things that are already known to be bad, an EDR program looks for suspicious behavior.
This is similar to having an intelligent security officer monitoring all activity within your office building. If the intelligent security officer sees someone attempting to barricade themselves inside multiple offices at once, he/she knows that someone is likely up to no good. Similarly, an EDR program will recognize when ransomware attempts to lock down all the “doors” in your “building,” and, once detected, will isolate the threat and stop the ransomware attack before it can encrypt your critical files.
By using EDR to protect your practice against ransomware attacks, you create a solid foundation for building robust, advanced, compliant HIPAA cybersecurity measures and add another layer of protection against employee errors.
Common HIPAA Cybersecurity Risks
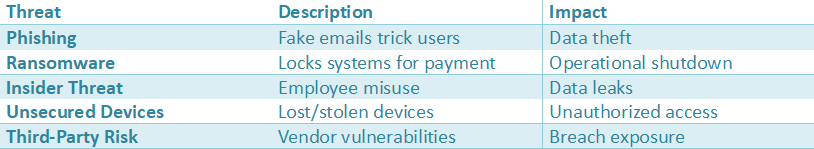
Insight: Most breaches stem from human error or weak access controls.
Source:
- Verizon Data Breach Report
https://www.verizon.com/business - FBI Cyber Division
https://www.fbi.gov
The Weakest Link: Holding Your Vendors Accountable with Business Associate Agreements (BAAs)
You invested considerable time and money into establishing your own private practice. How about your partners? You are probably using a billing company to assist you with billing, an answering service to answer phones, and a cloud-based Electronic Health Record (EHR) system to maintain and store all of your patients’ health records.
Each of these vendors has access to your patients’ highly sensitive and confidential information. Therefore, if one of them experiences a data breach, you can be held liable as well and potentially face HIPAA violations fines. This shared liability is based on the law set forth in the Business Associate Agreement (BAA).
A BAA is a written agreement that your business associate/vendor signs, which states that they agree to protect the confidentiality of your patients’ information in compliance with HIPAA rules and regulations. While signing a BAA is your vendor’s promise to protect your patients’ information, it is simply a promise. It does not provide proof that your vendor has implemented sufficient security measures to protect such information. Consider this analogy: Your vendor promises to lock their door. However, you do not know if they locked their door with a very weak padlock or a safe.
To meet today’s (Business Associate) Agreement Security Requirements, you will need to add an additional level of protection so that you may be able to obtain assurances from your vendors about their intent to protect your patients’ protected health information. These assurances often get in the way of independent audits or third-party certification to standards, including but not limited to NIST or HITRUST. These audit and/or certification results are well-known and generally accepted benchmarks for demonstrating strong HIPAA compliance and security.
You do not need a technical degree to evaluate your vendors. You merely need to know what to ask your vendors prior to entering into a contractual agreement with them that involves patient data. Before you enter into any contractual agreement that contains patient data, you should get specific responses regarding the following important issues:
- Could I get a copy of the last HIPAA Risk Assessment you conducted for our office?”
- “Do you do your own audit of your security processes (are you SOC 2 Certified or HITRUST Certified)?”
- “Will you notify me if there is a Security Incident that occurs with your company?”
If your vendor does not have clear, confident answers to these questions, that should raise major concerns. One of the best things you can do to keep both your patients safe and your practice safe from third-party threats is to ask your vendors these questions before signing up as their client.
Patient data protection: Explore strategies to keep healthcare records secure and private.

Protecting patient information is essential to prevent unauthorized access, enhance patient confidence in their healthcare providers, and enable Care Team members to access critical patient data at the right time. A well-planned Patient Data Protection plan helps reduce the risk of a breach by several avenues of attack, such as phishing, ransomware, internal errors, loss of mobile devices, and improper configuration of cloud applications. HIPAA Cybersecurity is one of many resources available for organizations to translate privacy expectations into real-world cybersecurity practices.
Implementing a comprehensive Patient Data Protection Plan begins by identifying the types of data your organization has and where they reside. This includes developing an inventory or “map” of all ePHI (Electronic Protected Health Information) contained within your Electronic Health Record (EHR), billing systems, scheduling systems, email, file shares, cloud-based applications, and backups.
This map will support your Risk Assessment efforts and allow HIPAA Cybersecurity teams to determine which areas need to be addressed first. Controlled documentation and monitoring of data sharing paths — especially those involving third-party vendors/business associates — will also help improve Patient Data Protection.
One of the most productive ways to enhance Patient Data Protection is through Access Control. By implementing Role-Based Permissions, only those individuals with appropriate permissions should have access to confidential patient information. Removing user accounts when roles or positions change within an organization; creating unique usernames for all users; utilizing multi-factor authentication for remote access, emails, and privileged accounts – these are commonly accepted HIPAA cybersecurity best practices. HIPAA Cybersecurity teams will be able to recognize unusual patterns in patient data access early on if they continuously log all activity.
A significant component of Patient Data Protection is encryption. This includes encrypting Sensitive Data both at Rest (i.e., servers, laptop computers, removable media) and in transit via secure communication protocols, which are required to protect confidential patient data under HIPAA regulations.
A compliant HIPAA Cybersecurity Program includes configuring hardware and network systems for security, ensuring that software applications are up to date, and performing ongoing vulnerability assessments to identify potential entry points into your system for hackers. In addition to protecting patient data, HIPAA-compliant organizations use endpoint protection and email security to prevent Malware and phishing attacks, which are the two most prevalent forms of cyberattacks used today to breach protected health information.
HIPAA Cybersecurity efforts are designed to prepare your organization to respond to data security breaches or other cyber-incidents that may occur, as well as those that have already occurred. In addition to this preparation, maintaining multiple isolated backup copies of all critical information and developing a solid incident response plan will equip you with the tools to quickly restore access to your organization’s information technology resources, patient records, and electronic medical record systems after an outage or ransomware attack.
Furthermore, training employees to properly handle protected health information (PHI), detect suspicious communication attempts via email and/or messaging platforms, and promptly report any potential PHI exposure will support both HIPAA Cybersecurity requirements and the protection of patient privacy. When Patient Data Protection is integrated into the routine business operations of healthcare providers/organizations, it will enhance the sustainability of HIPAA Cybersecurity and protect the confidentiality and integrity of patients’ personally identifiable information.
Health information privacy: Understand the importance of maintaining health information privacy to build trust and ensure regulatory compliance.

Protecting patient health information privacy is a core component of contemporary health care delivery. It provides patients with a safe space to express themselves about their health, treatment options, and life experiences when needed. Health Information Privacy also increases the likelihood that patients will report more accurately to clinicians, follow through on their established treatment plans, and use electronic devices such as patient portals and telemedicine services.
Health Information Privacy is important to compliance with federal statutes and state-specific regulations regarding the proper management of protected health information. In addition, there are formalized standards and processes for managing protected health information, as well as rules governing who has access to it and what is allowed and prohibited regarding its storage and distribution. HIPAA Cybersecurity is designed to enable organizations to effectively apply those standards and processes across all technologies used within their organizations.
Protecting Patient Health Information Privacy is a legal requirement. However, it also depends on establishing trust between patients and providers. A single occurrence of the unapproved disclosure of health information could cause significant harm to a patient’s reputation. Potential consequences include identity theft, financial exploitation, and social stigma. There is a direct link between protecting Patient Health Information Privacy and maintaining business continuity.
For instance, if a provider were to experience a system failure due to ransomware, it would likely lead to delays in providing appropriate patient care and create additional challenges in working around the operational issues resulting from the disruption. In these situations, the primary goal of HIPAA Cybersecurity is to minimize both unauthorized access to Protected Health Information and interruptions to business operations.
The first component is training the workforce to prevent unsafe sharing and identify phishing attempts. This helps to protect the privacy of an individual’s health information. With this training, they will be able to determine when there has been a breach of health information privacy and report it immediately.
HIPAA Cybersecurity programs support the workforce through Identity and Access Management (IAM), which includes Unique User Account Names, Role-Based Permissions, and Multi-Factor Authentication (MFA), so only employees authorized to review or modify sensitive patient records may do so.
As stated before, both technical and non-technical safeguards are necessary to protect the privacy of individuals’ health information. Technical safeguards include encrypting health information to prevent unauthorized disclosure during data transmission or storage on devices. Monitoring and audit logs help to detect potential security breaches early and reduce the risk of unauthorized disclosure of health information. In addition, using patches to manage risks and configuring all hardware and software used to store and transmit EPHI securely reduce the opportunities hackers have to exploit vulnerabilities in systems and devices.
Oversight of third-party vendors is also critical. Vendors use patients’ health information privacy as part of their services – whether it’s a billing service or software vendor – and must be evaluated and required to keep confidential any protected health information (PHI) accessed during their engagement with your practice. The HIPAA cybersecurity program enables organizations to establish and enforce technical and administrative controls to safeguard e-PHI. Further, the HIPAA cybersecurity program ensures that documentation is created and maintained for each control established and implemented.
Protecting people, rather than simply protecting data, is what health information privacy is all about. Therefore, developing strong policy language and implementing practical tools to apply these policies means establishing the practical HIPAA cybersecurity controls needed to earn patients’ trust, meet federal and state regulations, and create a culture where the protection of PHI is considered at all times throughout an organization’s workflow.
Your Action Plan: 7 Critical Questions to Ask Your IT Team This Week
To protect your patients and practice, you must act. While it may be difficult to assist with protecting your organization from cyber attacks, you do not have to be an expert to aid in doing so. All you need to do is know what questions to ask your IT Department or Vendor about your security this week. The following questions will begin a vital conversation about your organization’s present state of security. The responses to these questions will provide you with a visual picture of how far you are from being secure now and serve as a basis for conducting a HIPAA Risk Assessment.
Your response to each of the questions will show if your security exists on paper (and therefore complies), but does not defend against the types of threats that exist today.
- Does multifactor authentication (MFA) currently exist for ALL users across email, remote access, and electronic health record (EHR) systems?
- Are ALL of the company’s laptop, mobile device, and server data encrypted at this time?
- Can you tell me what the Company’s ransomware backup plan is — including when we last tested restoring from that backup?
- In addition to the traditional Antivirus protection provided by your antivirus software, are there any other forms of computer-based protection on your computers, such as Endpoint Detection & Response (EDR)?
- Approximately how often does the Company conduct simulated phishing tests for its employees using realistic scenarios?
- Have all vendors who come into contact with patients’ Protected Health Information (PHI) completed and signed a Business Associate Agreement (BAA)?
- Is there an Incident Response Plan (IRP), or step-by-step playbook, created and implemented within the Company for the occurrence of a Data Breach, and do all employees understand their specific role(s) in the event of a Data Breach occurring?
HIPAA cybersecurity checklist: Use this checklist to ensure your organization follows best security practices.

The HIPAA Cybersecurity Checklist is a tool designed to assist in confirming ongoing protection of Electronic Protected Health Information (ePHI) as well as in minimizing the risk of future breach(s) through adherence to established security practices and their repeated implementation. When used regularly, the checklist will convert regulatory compliance requirements into a systematic action plan that is easier to monitor, report on, and improve.
To establish a useful HIPAA Cybersecurity Checklist, it is essential to understand what you need to protect. First, identify all systems that have created, stored, or transmitted ePHI (e.g., EHRs, billing systems, patient portal applications, emails, cloud-based storage, endpoint devices, backup media, etc.), then map out where these systems send the data you collect.
Document which individual or department owns each identified system. Finally, establish if your organizations policies and procedures regarding employees’ education/training, as well as technical security controls implemented to protect those systems align with the present day environment—versus how they may have been last year.
Begin your HIPAA Cybersecurity Checklist by completing Risk/Governance Items:
- Perform a current risk analysis that has been documented, along with a written risk management plan that contains priority remediation for identified risks.
- Create an updated list of Security Policies (Access, Remote Work, Devices, Data Sharing, Incident Response) and update it as needed.
- Provide ongoing training to all employees regarding these security topics and document the date each employee completes this training.
Complete the HIPAA Cybersecurity Checklist to ensure you are utilizing Access Control/Authentication Controls:
- User IDs should be unique, Role-Based Permissions should be used to limit access, and User IDs should be terminated quickly if Staff Members Change Roles.
- Multi-Factor Authentication is required for Remote Access, Email, and Admin Accounts.
- Regularly Review Privileged Access & Shared Account(s) and reduce/eliminate them whenever possible
Then you should look over your HIPAA Cybersecurity checklist for “core technical safeguards,” which include the following items:
- Data encryption while transporting information, and if applicable, when stored at rest on an endpoint and/or portable media.
- Patch Management, Secure Baseline Configurations, and Vulnerability Scanning with fix tracking.
- Centralized Logging/Monitoring, in addition to regular audits of log entries, looks for Unusual Access.
- Backup(s) that can be isolated/Immutable wherever possible; backup(s) tested to ensure they will restore properly; and protected against Ransomware.
You should then conduct a HIPAA Cybersecurity checklist review using a predetermined schedule (e.g., monthly or every quarter) upon occurrence of significant changes (i.e., new vendor, system migration, merger, or incident); and consider this document a Living Document: update controls, maintain documentation; and address gaps prior to becoming Reportable Events.
HIPAA Cybersecurity Checklist
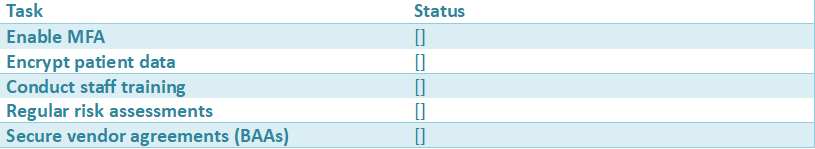
Key Insight: A simple checklist helps organizations move from compliance to real security.
Source:
- HHS HIPAA Compliance Guide
https://www.hhs.gov/hipaa - NIST Cybersecurity Framework
https://www.nist.gov
From Checkbox Compliance to Digital Resilience: Making Security Part of Patient Care
HIPAA Security is not just an information technology issue but also a patient safety issue. HIPAA Security policy examples include an organization with a policy that encrypts all laptops in its possession; even if someone steals one, the organization has complete confidence in its ability to protect the privacy of any PHI on it. Secondly, another example is multi-factor authentication (MFA): if an organization uses MFA for access to electronic phil (e-phil), no unauthorized person will be able to disrupt or alter scheduled appointments. Understanding this helps transform the dialogue about HIPAA Security from theoretical risks to real concerns of patient care.
By focusing on patient care, this approach can help organizations develop true resilience and build an active defense against data breaches by implementing smart, layered defenses and training teams to understand why those layers are as important as sterile processing and cleaning medical equipment. Finally, this approach can transform HIPAA Security from a barrier to entry into a core part of your business strategy.
To get started leading this type of change, you should take one action – ask your IT team the right questions today. Use the action plan above to start the dialogue with your it team today. By taking this single step, you are making a direct, tangible investment in what really matters to your patients – uninterrupted quality care and continued, unshakeable trust they place in you.
Conclusion
HIPAA Cybersecurity for Healthcare Organizations — Building Resilience & Trust. The authors argue that healthcare organizations must protect patient safety AND business continuity through effective, compliant HIPAA cybersecurity practices. The HIPAA Security Rule is not simply a paper exercise. It outlines specific real-world practices that ensure Electronic Protected Health Information (ePHI) remains secure, protects against downtime, and maintains patient confidence during actual cyberattacks (such as phishing or ransomware).
In summary, the article argues that building resilience involves developing multiple, simple-to-verify-and-maintain layers of impact controls. Multi-factor authentication can limit account takeover attacks, and encrypting data on devices ensures that if an unencrypted device is lost or stolen, it cannot be reported as a breach. Current Endpoint Protection systems can prevent ransomware attacks from spreading.
However, equally important is the need for continuous, relevant employee training to create a ‘Human Firewall’ that limits the likelihood that a single employee’s failure could cause a crisis. Furthermore, the article states that security does not exist behind your four walls; therefore, it is vital to hold Vendors/Partners responsible for their security practices via updated Business Associate Agreements and regular Security Reviews/Audits.
Finally, the article’s last call to action is to encourage Leaders to act NOW and begin asking targeted questions, confirming the implementation of the most critical safeguards, testing backups and Disaster Recovery Plans, and making Cybersecurity an ongoing part of delivering care rather than an annual compliance activity.
FAQs
1) What’s the difference between the HIPAA Privacy Rule and the HIPAA Security Rule?
The Privacy Rule defines how PHI may be used or disclosed, whereas the Security Rule describes how ePHI must be safeguarded through the implementation of physical, administrative, and technical measures to protect against unauthorized disclosure, modification, or destruction.
2) Why is multi-factor authentication (MFA) so important for HIPAA cybersecurity?
MFA provides a second level of verification beyond a user ID and password, preventing unauthorized access to accounts even if a hacker has obtained the credentials. MFA should be implemented for email, remote access, and EHR logon, as these represent common points of entry for hackers.
3) How does encryption help with HIPAA compliance if a device is lost or stolen?
For encryption to effectively protect ePHI on laptops, drives, servers, etc., it must be applied to the data itself so it cannot be read without the decryption key. For example, in many instances, where a laptop containing encrypted ePHI is lost, the data will likely not constitute a reportable breach, thereby minimizing notification requirements and potential damage to the organization’s reputation.
4) Why isn’t annual HIPAA training enough to prevent cyber incidents?
Phishing attacks evolve regularly, and staff tend to forget previously provided training. Repeatedly providing short, ongoing training sessions, combined with simulating phishing “attacks” in practice, builds real-world skills and awareness among staff to recognize time-sensitive scams, mismatched senders, and unsafe links that could lead to an incident.
5) Are Business Associate Agreements (BAAs) enough to manage vendor risk?
While a BAA is mandatory, it is merely a contractually agreed-upon obligation. An organization should also verify its vendors by requesting documentation of their security practices (e.g., risk assessments, incident reporting, and independent audit reports [such as SOC 2 or HITRUST]) to reduce the likelihood of a vendor-caused breach.